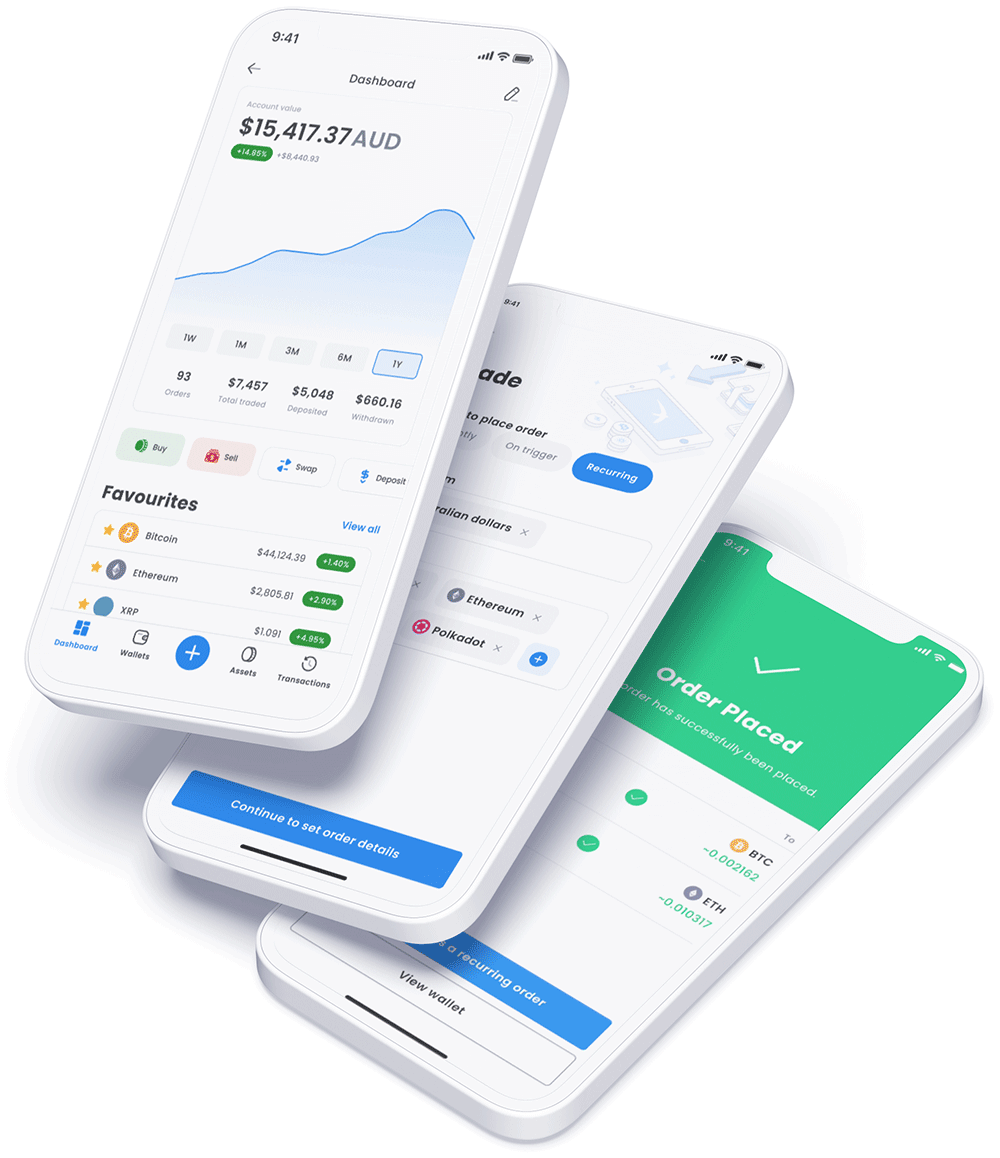
Buy crypto in minutes
- Signup for free
- Verify your account
- Fast AUD Deposits
- Start trading 320+ cryptocurrencies
Official partner of
![]() withdrawals & deposits
withdrawals & deposits
owned and operated
assets for trading
on *
Swyftx is an AUSTRAC registered digital currency exchange headquartered in Brisbane, Australia.
Swyftx holds ISO27001 certification which is internationally recognised for information security.
Your assets and funds are protected through multi-layer technology and advanced security frameworks.
Our Australian-based support team are here to answer all your questions and help you navigate the Swyftx platform.
Test your strategies and learn the market without committing your own money with our demo mode.
Diversify your cryptocurrency portfolio and purchase multiple assets with just one single trade.
Be rewarded with crypto and other special offers by actioning certain tasks within the Swyftx platform.
Deposit funds easily into your account via a number of payment methods, some of which are processed instantly.
Set up recurring deposits and have orders automatically trigger across a range of assets.
Utilise technical indicators and tools to track and analyse your preferred assets with our TradingView charts.
Stay up to date on the latest news and trends in the market by accessing real-time news from numerous publications.
Invest in cryptocurrencies through your company, trust, or SMSF and keep track of your investments in a single location.
View detailed “how to” guides and instructions on navigating the Swyftx platform and using specific features.
Send your question via live chat and we’ll reply with a helpful answer - under 10 minutes.
Access quality educational resources and expert market analysis to sharpen your crypto and blockchain knowledge.
Listen to the Tapping into Crypto podcast for the latest trends and opportunities in cryptocurrency.